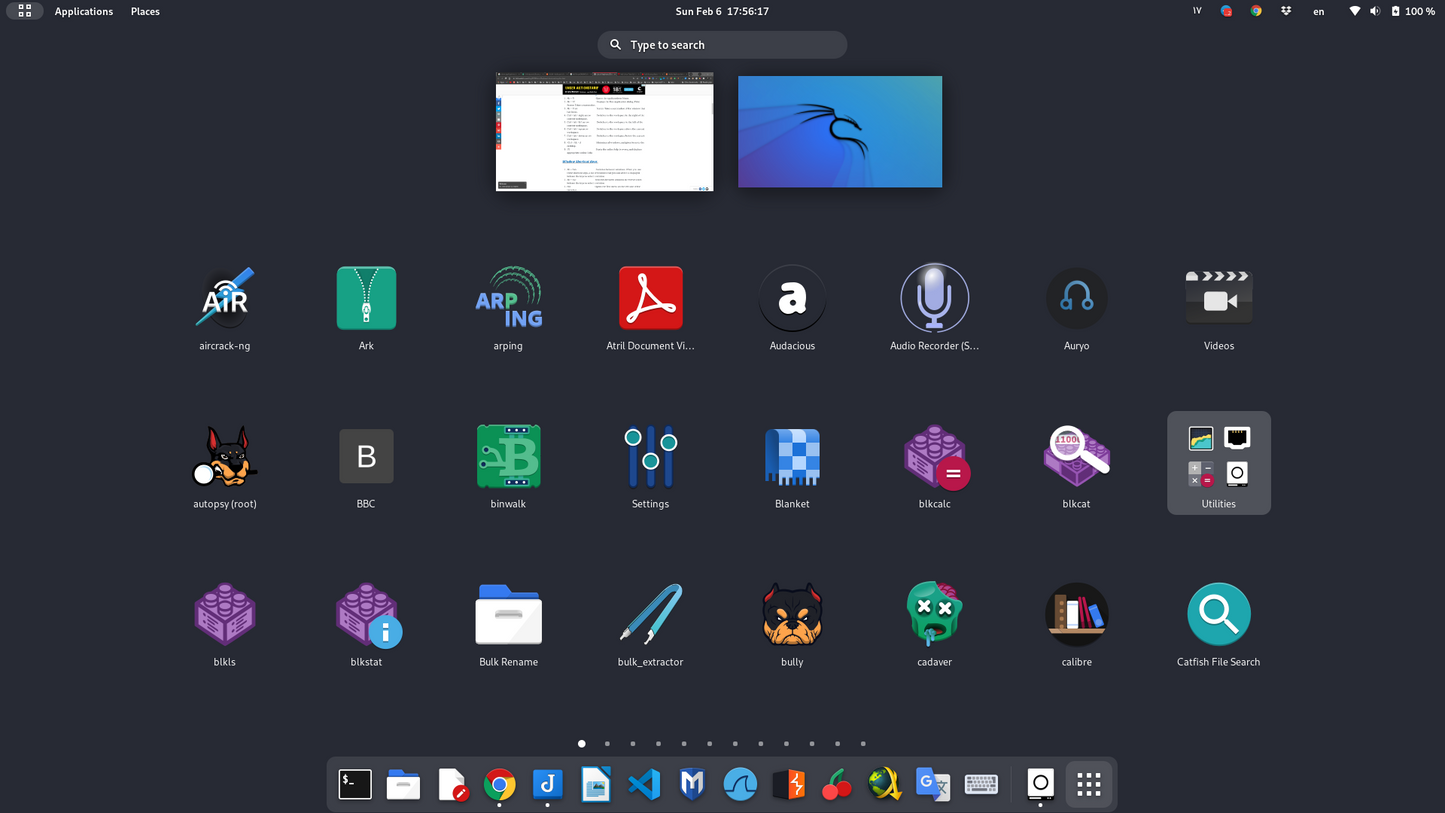
Kali Linux Bootable USB – Ethical Hacking & Cybersecurity Operating System
Kali Linux Bootable USB – Ethical Hacking & Cybersecurity Operating System
Couldn't load pickup availability
Boot Kali Linux from USB for security auditing, penetration testing training, and incident response — no installation required. Run it Live to test networks and systems you own or are authorized to assess, or install to disk when you’re ready.
Why Kali?
- Purpose-built for security: curated tools for auditing, reconnaissance, and analysis.
- Portable lab: boot anywhere without altering the host OS.
- Learning-friendly: great for courses, homelabs, and certification prep.
- Installable: optionally install to internal storage for a permanent setup.
📦 Package / What’s Included
- Bootable Live USB (dual USB-A/USB-C connector) with Kali pre-flashed.
- Quick-start guide: boot keys, Wi-Fi tips, and update basics.
- Optional packaging: standard bubble mailer or gift tin case (select above).
💻 Compatibility & Requirements
- Systems: 64-bit (x86_64) PCs that can boot from USB (UEFI or Legacy BIOS).
- RAM: 4 GB+ recommended (8 GB+ for heavy tools).
- Storage (optional install): 25 GB+ free space suggested.
- Secure Boot: some devices may require disabling Secure Boot for external media.
- Not for ARM-only Macs (M1/M2/M3).
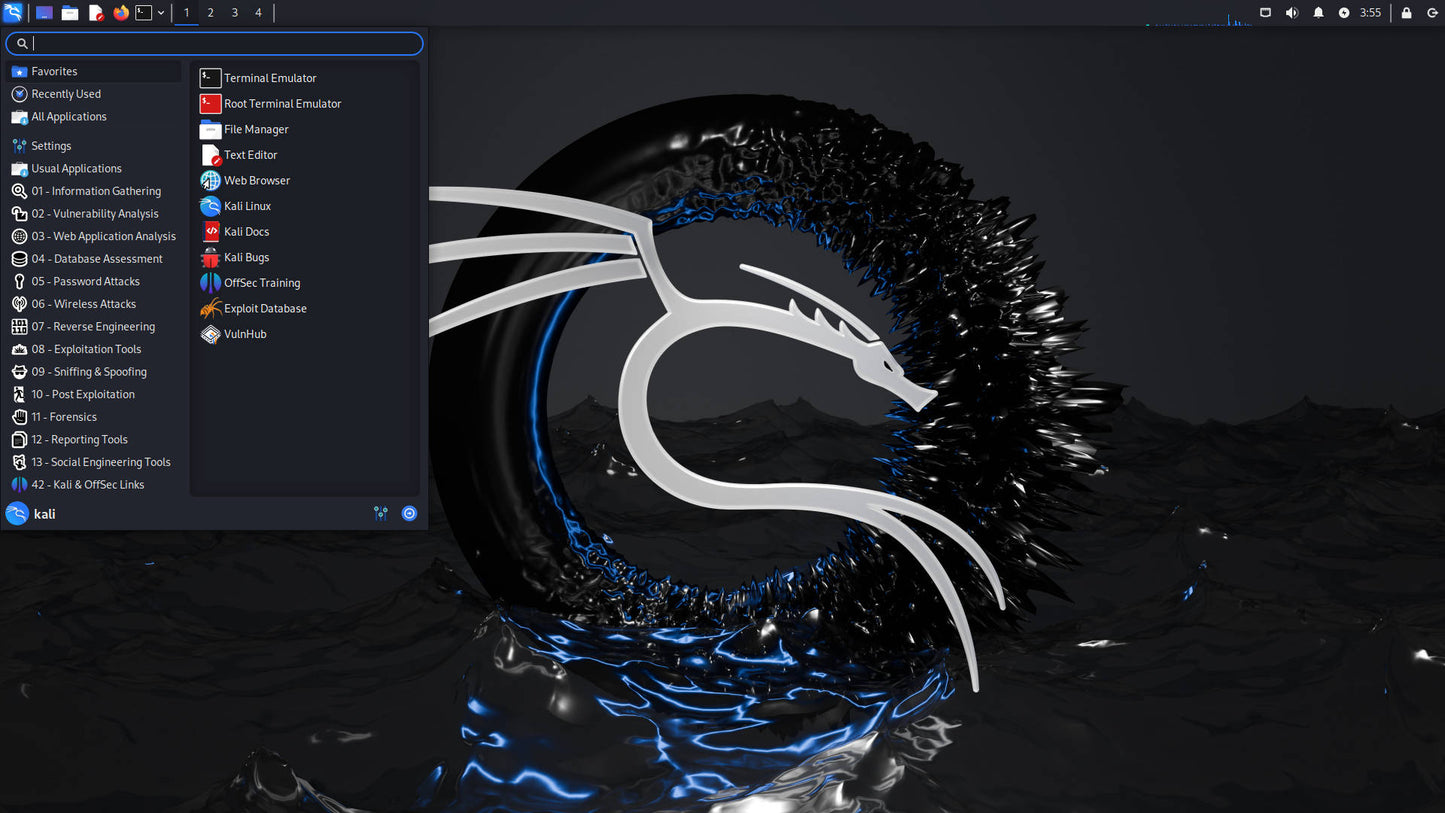
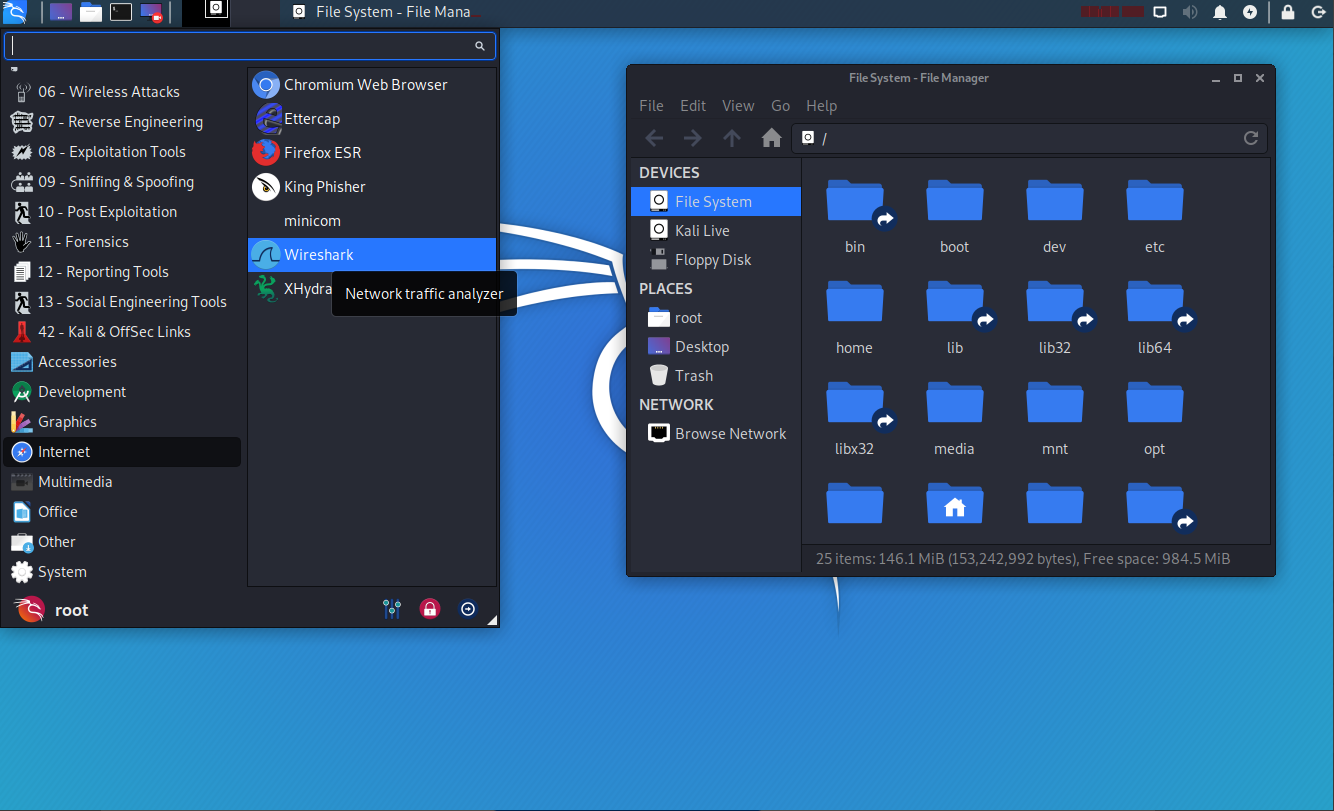
🧰 Typical Tool Categories
- Recon & scanning: network discovery, service enumeration.
- Web & app testing: proxying, fuzzing, analysis.
- Wireless assessments: capture/analysis with compatible adapters.
- Passwords & forensics: offline analysis tools for lawful workflows.
- Exploit development & reverse engineering: debuggers, disassemblers, build chains.
Adapter note: Some wireless tools require specific chipsets and drivers; a compatible USB Wi-Fi adapter may be needed for monitor/injection modes.
⚙️ How to Boot
- Insert the USB, power on, press your boot-menu key (F12, Esc, F10, F2, etc.).
- Select the USB device and start the Live environment.
- Test hardware, connect to network, and run tools. Install later if desired.
Help & Tutorials — boot keys, USB booting tips, and troubleshooting.
🛡️ Legal / Ethical Use
- Use only on systems and networks you own or have explicit written permission to assess.
- Follow all laws, regs, company policies, and class rules where applicable.
- For production environments, coordinate with stakeholders and change windows.
🛠️ Support
Questions about booting or wireless adapter compatibility? Message Us
Ethical & Legal Use
This product is intended for lawful training, testing, and incident response. You are responsible for compliance with all applicable laws and for obtaining authorization before testing.
Share